Underlay and Overlay Networking
Mechanical Engineer by qualification with a strong passion for technology and networking. CCIE Routing & Switching and Security (#22239, since 2008). Former Cisco TAC, HP, and Wipro. Currently focused on building free, impactful tools for India. Ongoing projects include Namohos.com, Anantaos.com, and Freefreecv.com.
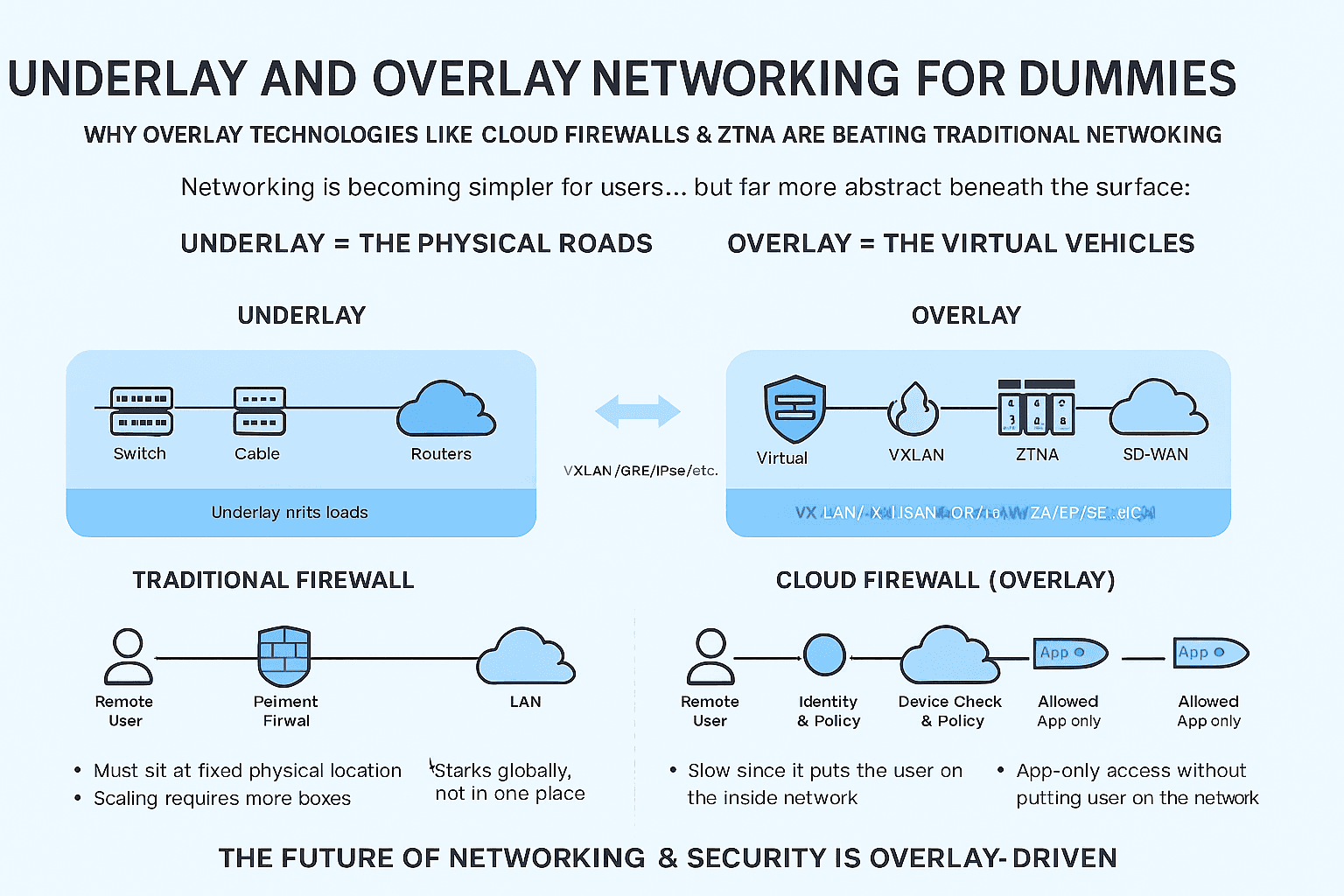
Why Overlay Technologies Like Cloud Firewalls & ZTNA Are Beating Traditional Networking**
Networking is becoming simpler for users… but far more abstract beneath the surface.
Cloud, virtualization, SDN, SASE, ZTNA, and cloud firewalls all depend on one idea:
Overlay networking.
To understand why these modern technologies are winning, you only need to understand two concepts:
Underlay = the physical roads
Overlay = the virtual vehicles
Let's break it down with simple visuals.
1. What Is an Underlay?
Underlay = the physical network.
It includes:
Cables
Switches
Routers
Physical routing protocols (OSPF, BGP, etc.)
Physical IP addressing
Think of it like the physical road network beneath a city.
┌───────────┐ ┌───────────┐
│ Switch │-------│ Router │
└───────────┘ └───────────┘
| |
┌───────────┐ ┌───────────┐
│ Cable │-------│ Switch │
└───────────┘ └───────────┘
If the underlay breaks, nothing works.
But the underlay does not decide:
who can talk to whom
how traffic is segmented
how firewall policies are applied
how security is enforced
It only forwards packets.
2. What Is an Overlay?
Overlay = a virtual network built on top of the underlay.
Think of it like Uber, Ola, or Google Maps running over the same physical roads—but controlling the route, access, identity, etc. through software.
┌─────────────────────────── Overlay (Virtual) ──────────────────────────┐
│ │
│ Virtual Firewalls VXLAN ZTNA SD-WAN SASE │
│ │
└─────────────────────────────────────────────────────────────────────────┘
┌──────────────────────── Underlay (Physical) ───────────────────────────┐
│ Switches │ Routers │ Fiber │ Cables │ Routing Protocols │ Connectivity │
└────────────────────────────────────────────────────────────────────────┘
Overlays don’t care about physical location.
They create:
Virtual networks
Virtual firewalls
Virtual tunnels
Virtual topologies
Virtual segmentation
This is why cloud networking works anywhere.
3. Underlay vs Overlay in One Simple Diagram
┌─────────────────────────┐
│ Overlay │
│ (Policies, Security, │
│ Routing, Segmentation)│
└──────────┬──────────────┘
│ VXLAN/GRE/IPsec/etc.
┌──────────┴──────────────┐
│ Underlay │
│ (Switches, Cables, IPs) │
└──────────────────────────┘
Overlay = logic
Underlay = plumbing
4. Why Overlays Are Winning
Modern networking challenges can’t be solved by physical networks alone.
Traditional networking was limited by:
location
physical hardware
VLAN boundaries
firewall choke points
static perimeters
The world changed:
Apps are global
Users work remotely
Workloads run in multiple clouds
Microservices scale dynamically
Zero Trust demanded identity-aware security
The underlay can’t solve any of this.
Overlays solve all of it.
5. Cloud Firewall vs Traditional Firewall
Traditional Firewall (Old Way)
┌─────────────────────────────────┐
│ Perimeter Firewall │
└───────────────┬─────────────────┘
LAN
(Inside the office)
Challenges:
Must sit at a fixed physical location
All traffic must pass through it
Remote workers need VPN
Limited visibility beyond perimeter
Hardware failures = outage
Scaling requires more boxes
Cloud Firewall (Overlay Way)
┌───────────────────────────────────────────┐
│ Cloud Firewall Overlay │
│ (SASE / FWaaS / NGFW / Identity-Aware) │
└────────────┬────────────┬────────────┬────┘
│ │ │
Branch Remote Cloud VMs
Office Users & Apps
Benefits:
Not tied to any location
Policies follow the user, not the network
Ingress/egress can happen globally
No hardware to maintain
Auto-scales
Integrates with identity, device posture, risk signals
Perfect for multi-cloud
Cloud firewalls live in the overlay world.
That's why they're winning.
6. ZTNA vs VPN
VPN (Old Underlay-Dependent Model)
Remote User → VPN → Inside Network (Full Access)
Problems:
User becomes part of the internal subnet
High lateral movement risk
Slow (all traffic hairpins)
Works poorly for SaaS
Relies on IP-based trust
ZTNA (Overlay Model with Identity)
Remote User
│
▼
Identity + Device Check + Policy
│
▼
Allowed App Only (Not the whole network)
┌─────────────────────────────┐
│ ZTNA │
│ (App-level connectivity) │
└────────┬──────────┬────────┘
│ │
App A App B
ZTNA uses an overlay to create per-app tunnels, not full network access.
7. Why Overlays Beat Traditional Networking
1. Identity > IP Address
Overlays use:
identity
user
device posture
application
risk signals
Traditional firewalls use:
IP
port
protocol
Identity-based security is dramatically stronger.
2. Location No Longer Matters
Apps, users, and workloads move.
Overlays adapt within seconds.
3. Infinite Scalability
Underlay has physical limits.
Overlay scales with compute.
4. Multi-Cloud Requires Overlays
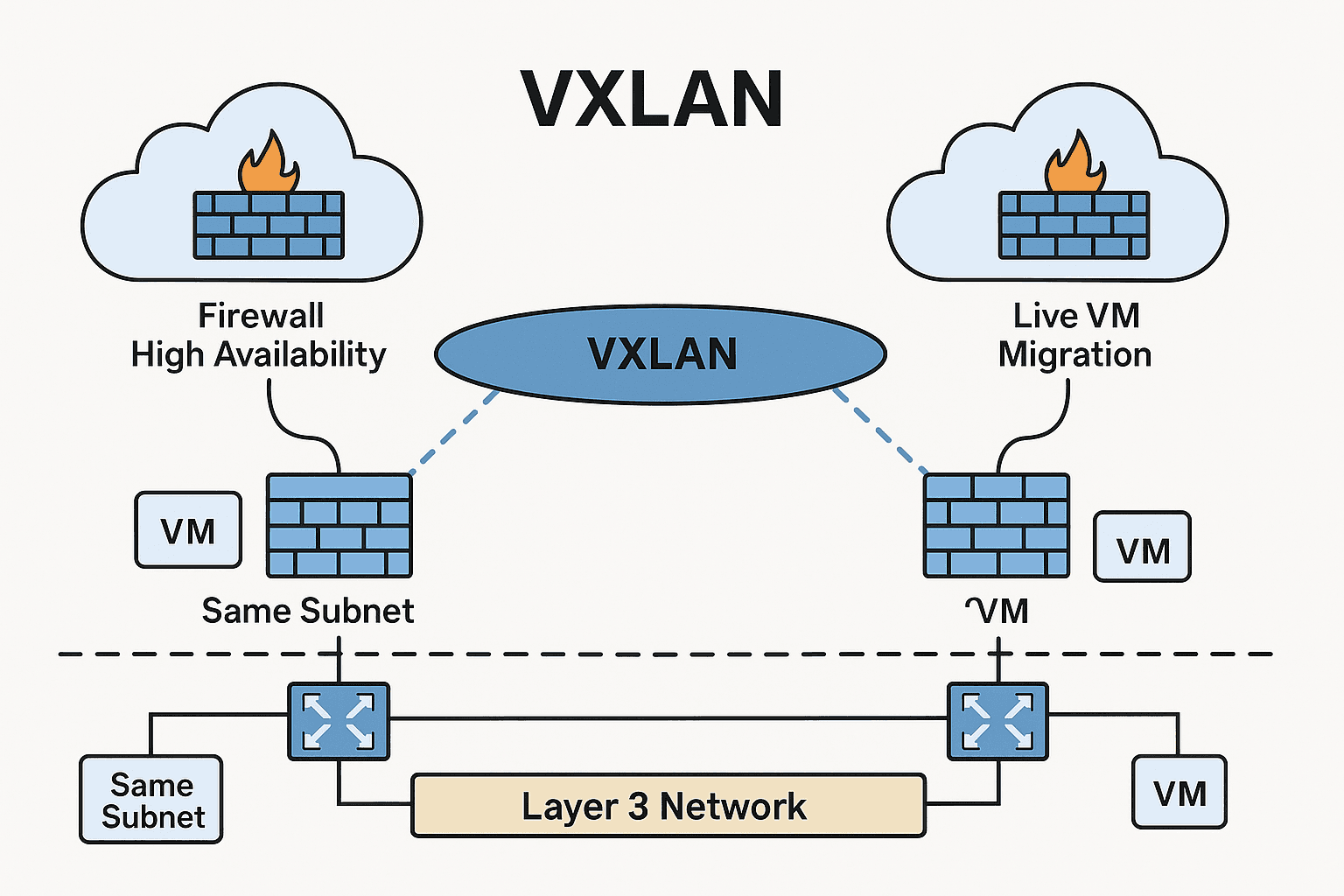
AWS, Azure, and GCP cannot stretch VLANs.
But overlays (VXLAN, Geneve, SD-WAN, ZTNA tunnels) work everywhere.
5. Zero Trust Is Only Possible in Overlay
Because policies follow the identity, not the cable.