Best Cyber Security Courses and Certificates 2025

Launch Your Cyber Security Career with Networkers Home
In today’s digital world, how safe is your data? As cyber threats grow, mastering cybersecurity is more important than ever. Ready to secure your future? Enroll in the Best Cyber Security Courses and Certificates in 2025 and gain the skills to protect critical systems from attacks.
At Networkers Home, our Cyber Security Courses provide hands-on experience in defending networks and securing data. With businesses needing skilled professionals, can you afford to miss out? Start your cybersecurity journey now and position yourself for success in one of the most in-demand fields today!
What You Will Learn in Our Cyber Security Course
Our Cyber Security Course offers a comprehensive journey from foundational knowledge to advanced defense techniques. Here's a sneak peek into what you’ll learn:
1. Introduction to Cybersecurity
Overview of Cybersecurity: Understand the critical role cybersecurity plays in protecting data and systems in the digital age.
Key Terminology and Concepts: Familiarize yourself with essential terms like threats, vulnerabilities, and risks—the core building blocks of cybersecurity.
Cybersecurity Threat Landscape: Explore various cyber threats, including viruses, ransomware, and advanced attacks like APTs, and understand their impact on businesses and individuals.
2. Cyber Threats and Attacks
Types of Cyber Threats: Dive into the various types of cyber threats such as viruses, malware, ransomware, and phishing. Understand how each one operates and its potential damage to systems and data.
Advanced Persistent Threats (APT): Learn the tactics used in APTs, which involve long-term, targeted attacks by skilled adversaries, and discover the defense strategies to counter them.
Case Studies of Major Cyber Attacks: Analyze real-world cyber-attacks like those on major corporations or governments to understand the causes, impact, and key lessons for improving security protocols.
3. Cybersecurity Frameworks and Standards
NIST Cybersecurity Framework: Understand the structure and application of the NIST Cybersecurity Framework, a globally recognized approach to managing cybersecurity risks.
ISO/IEC 27001 and 27002: Explore the ISO standards for establishing and maintaining effective information security management systems (ISMS) to safeguard sensitive data.
Other Cybersecurity Standards: Learn about various other standards like SOC 2, PCI-DSS, HIPAA, and GDPR, which help organizations comply with industry regulations and protect data privacy.
4. Network Security
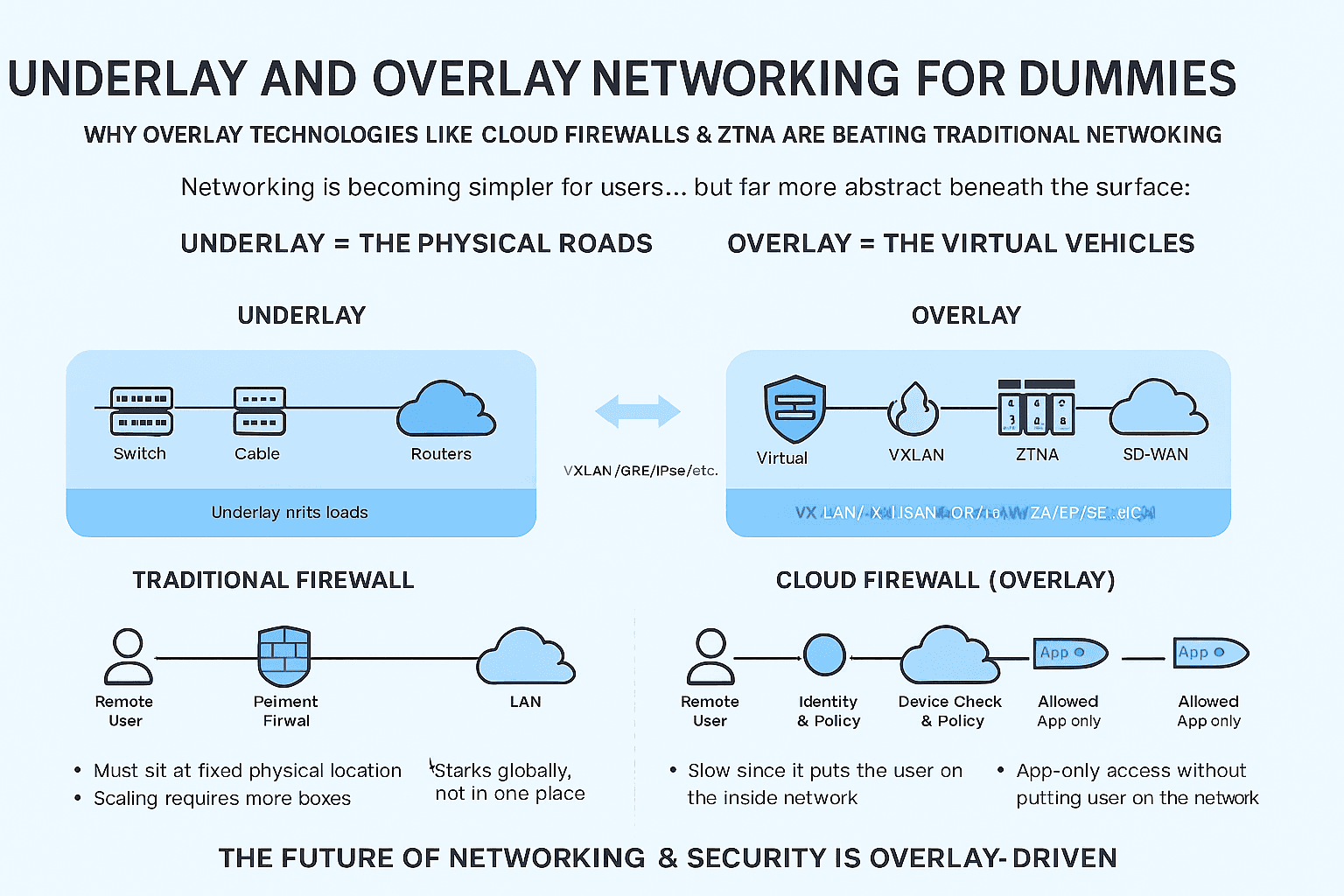
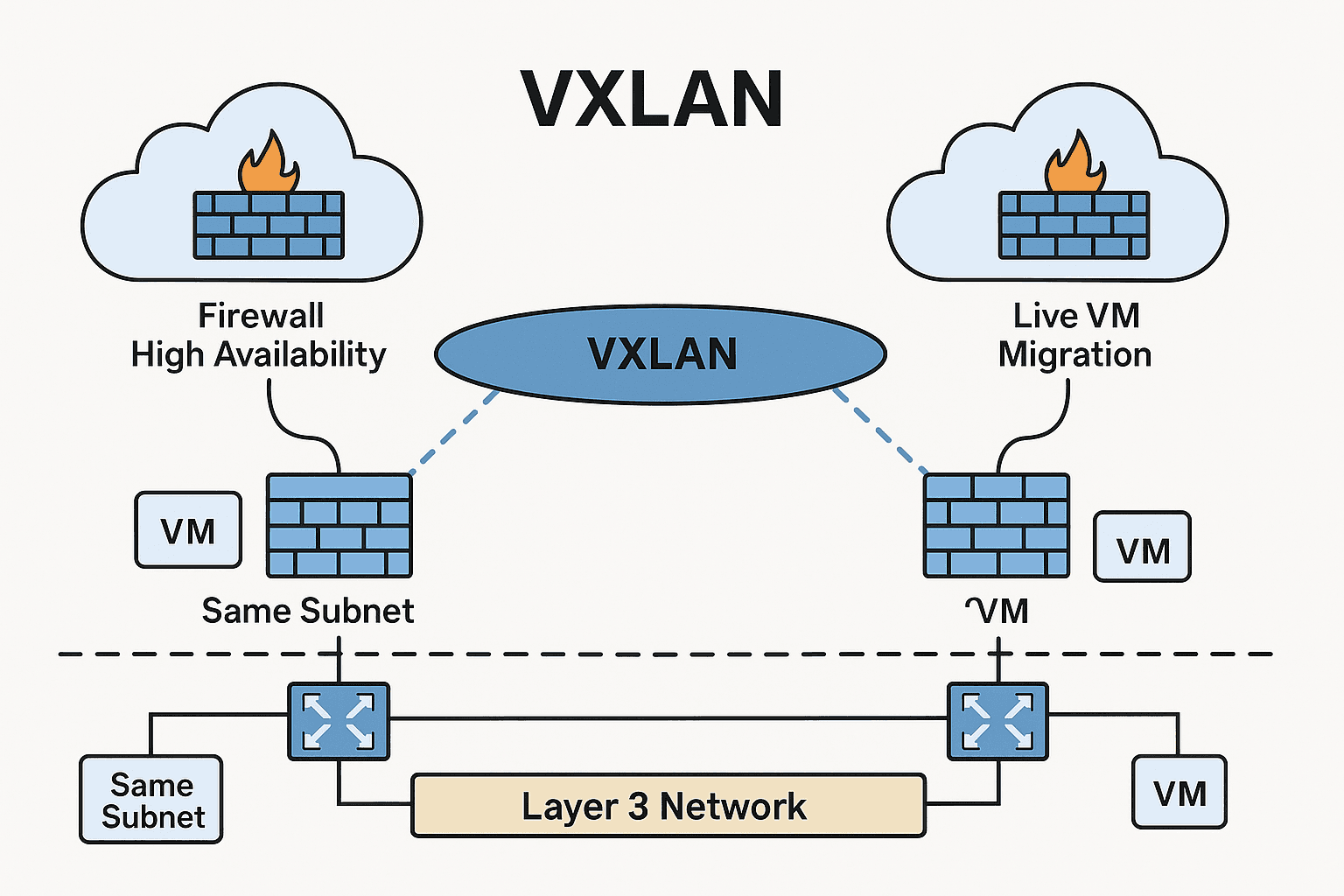
Principles of Network Security: Understand how to secure networks against unauthorized access, breaches, and attacks using fundamental security principles.
Firewalls, VPNs, and IDS/IPS: Master the configuration and management of firewalls, Virtual Private Networks (VPNs), and Intrusion Detection/Prevention Systems (IDS/IPS) to enhance network protection.
Network Monitoring and Analysis: Develop skills in monitoring network traffic and analyzing data to identify and respond to potential security incidents in real-time.
5. Cryptography and Data Protection
Introduction to Cryptography: Learn the basics of cryptographic techniques such as encryption and decryption to secure data transmission and storage.
Public Key Infrastructure (PKI): Understand the role of PKI in securely exchanging information over the internet through encryption and digital certificates.
Data Loss Prevention (DLP): Explore strategies and tools for protecting sensitive data from leaks or theft, ensuring it remains secure across systems and devices.
6. Cloud Security
Introduction to Cloud Computing: Gain insight into cloud environments like IaaS, PaaS, and SaaS, and understand their unique security risks and challenges.
Cloud Security Risks: Identify the potential threats in cloud computing, including data breaches and insecure APIs, and how to mitigate these risks.
Best Practices for Securing Cloud Services: Learn industry best practices for securing cloud infrastructures, such as encryption, identity and access management (IAM), and proper configuration.
7. Identity and Access Management (IAM)
Importance of IAM in Cybersecurity: Explore how IAM systems manage user access to critical data and applications, ensuring only authorized individuals gain access.
Authentication Mechanisms: Understand the various authentication methods like passwords, multi-factor authentication (MFA), and biometrics, which secure user logins.
Role-Based Access Control (RBAC): Learn how RBAC assigns system access based on users' roles within an organization, limiting access to sensitive information based on job function.
8. Incident Response and Management
Incident Response Life Cycle: Discover the phases of an incident response, including detection, containment, eradication, and recovery, to effectively respond to cyber-attacks.
Creating an Incident Response Plan: Learn the key components of a robust incident response plan, which ensures a timely and organized approach to security breaches.
Forensics and Investigation: Develop the skills to conduct digital forensics, gathering and analyzing evidence to determine the cause and impact of a breach.
9. Ethical Hacking and Penetration Testing
Introduction to Ethical Hacking: Understand the role of ethical hackers in testing and strengthening systems by simulating cyber-attacks to find vulnerabilities before malicious actors exploit them.
Penetration Testing Methodologies: Learn the methodologies used in penetration testing, including planning, reconnaissance, exploitation, and post-test reporting.
Legal and Ethical Considerations: Gain knowledge of the legal and ethical standards that guide penetration testing, ensuring hacking activities remain within lawful boundaries.
10. Cybersecurity in Emerging Technologies
IoT Security: Explore the unique security challenges posed by the Internet of Things (IoT), including device vulnerabilities and network security concerns.
AI and Machine Learning in Cybersecurity: Learn how artificial intelligence (AI) and machine learning are being leveraged to identify and respond to cyber threats more efficiently.
Blockchain and Security: Understand the potential of blockchain technology in enhancing cybersecurity, particularly in securing transactions and protecting data integrity.
11. Security Governance and Risk Management
Risk Management Framework: Learn how to assess, manage, and mitigate cybersecurity risks within an organization, helping to prioritize resources and actions based on potential threats.
Governance, Risk, and Compliance (GRC): Understand how GRC strategies are applied to ensure organizations remain compliant with regulatory requirements while managing security risks.
Business Continuity and Disaster Recovery: Learn how to plan for cybersecurity resilience, ensuring that businesses can quickly recover and maintain operations after an attack or system failure.
12. Hands-on Labs and Practical Sessions
Network Security Simulation: Gain practical experience by configuring firewalls, VPNs, and IDS systems in a controlled lab environment to strengthen your network security skills.
Penetration Testing Lab: Apply your knowledge of ethical hacking and penetration testing tools in real-world scenarios to identify and exploit vulnerabilities in test environments.
Incident Response Simulation: Engage in real-time simulations of security breaches, practicing your response strategies and developing the skills to manage cyber incidents effectively.
Career Opportunities After Completing the Cyber Security Course
Upon completing our Cyber Security Course and earning your Cyber Security Certification, you’ll be fully prepared to explore a range of exciting career paths in this fast-growing field:
Cybersecurity Analyst: Protect organizations from evolving cyber threats by monitoring systems, analyzing vulnerabilities, and implementing security measures to safeguard critical assets.
Penetration Tester (Ethical Hacker): Use your expertise to simulate cyberattacks, identify weaknesses in systems, and help organizations strengthen their defenses before malicious hackers can strike.
Network Security Engineer: Ensure robust network protection by designing, implementing, and managing secure network infrastructures, preventing unauthorized access and cyberattacks.
Cloud Security Specialist: Focus on securing cloud environments, managing risk, and implementing best practices to protect sensitive data stored and processed in the cloud.
Incident Response Specialist: Lead the charge in identifying, responding to, and mitigating security breaches, ensuring swift recovery and minimizing the impact of cyberattacks.
With cybersecurity in demand across industries like finance, healthcare, government, and technology, these cyber security certifications will open doors to high-paying, rewarding career opportunities.
Why Choose Networkers Home for Your Cyber Security Training?
At Networkers Home, we’re dedicated to providing you with the best Cyber Security courses and certifications that will equip you with the skills needed to tackle real-world cyber threats. Our expert instructors, who bring years of hands-on experience, ensure you receive top-notch training designed to meet the demands of the ever-evolving cybersecurity landscape. We focus on a practical, results-driven approach, making sure that you don’t just understand theoretical concepts but also know how to apply them in real-world scenarios.
With our cutting-edge curriculum aligned with global standards, we empower you to become a cybersecurity professional who can handle any challenge. Our hands-on labs allow you to practice in a simulated environment, refining your skills and boosting your confidence. At Networkers Home, we are committed to your success, helping you build a strong foundation and enhancing your employability in a rapidly growing field. Ready to take your cybersecurity career to the next level? We’re here to help you make it happen!
Conclusion
In today’s digital age, cybersecurity is no longer a luxury—it's a necessity. Choosing Networkers Home for your Cyber Security Course positions you at the forefront of one of the most in-demand fields. With expert instructors, hands-on labs, and a comprehensive curriculum, we ensure you gain the skills and certifications needed to tackle cyber threats and secure critical systems. Whether you're starting your cybersecurity journey or looking to level up your career, our courses are designed to meet your unique needs and provide you with real-world experience.
Don't wait for a cyber threat to catch you off guard—enroll today at Networkers Home and start building the expertise needed to protect data, systems, and networks in the face of ever-evolving cyber risks. Secure your future with the best Cyber Security Courses and Certifications in 2025, and unlock high-paying, rewarding career opportunities in industries like finance, healthcare, government, and tech. Visit Networkers Home now to take the first step toward becoming a cybersecurity professional who can make a real impact!