🔒 Elevate Your Network Security Knowledge with Zero Trust Network Access (ZTNA) 🔒
Ever heard of Zero Trust Network Access (ZTNA)? It's not just another tech buzzword – it's a game-changer in the realm of cybersecurity. 🚀
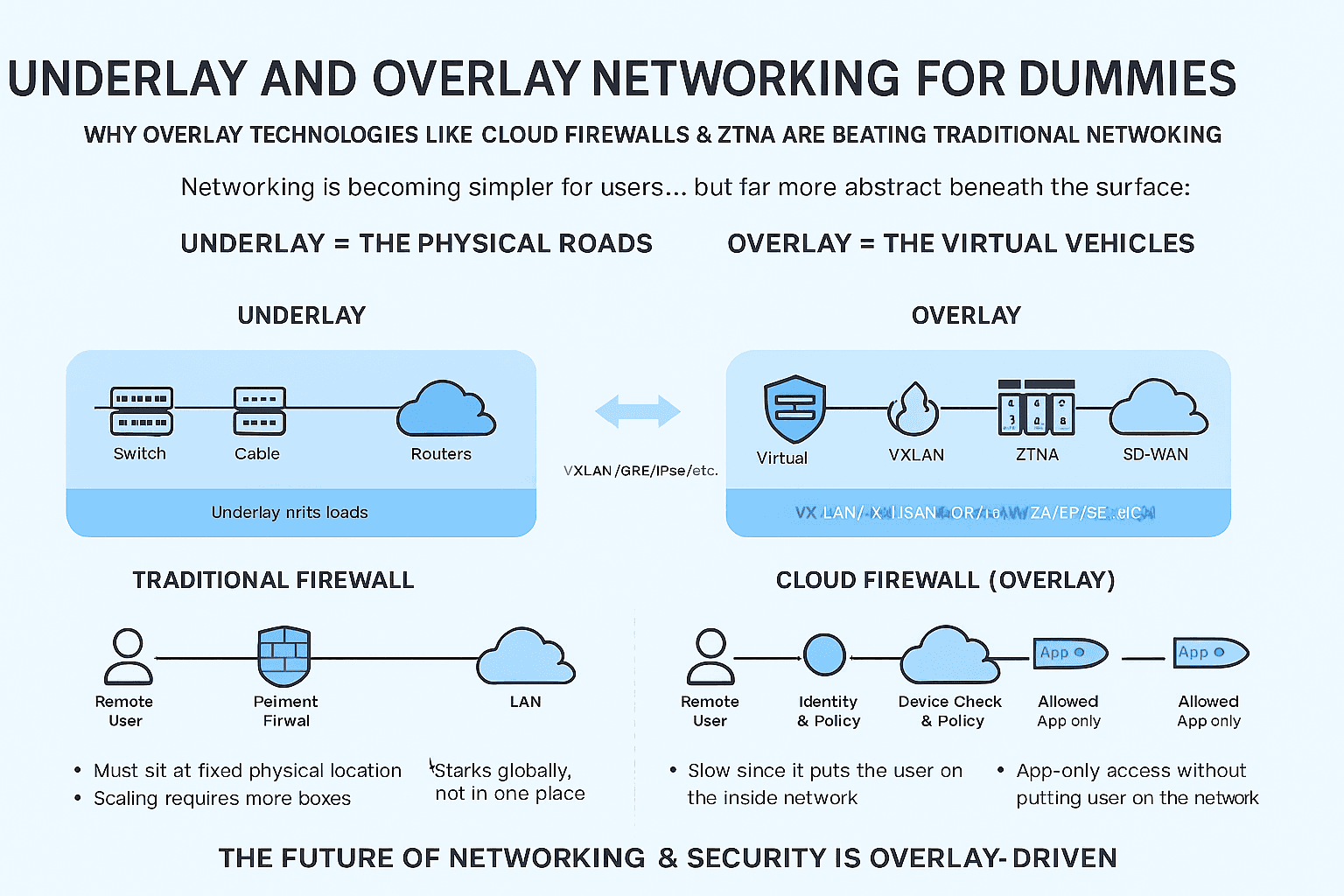
🔐 What's ZTNA All About? ZTNA flips the script on traditional security models. It's all about challenging assumptions and embracing a new mindset. Instead of blindly trusting everything inside your network's perimeter, ZTNA assumes that nothing is inherently safe.
🛡️ Why Should You Care? As fresh network engineers, understanding ZTNA is like having a secret weapon in your cybersecurity arsenal. It's all about tight access controls, multi-factor authentication, and dynamic policies. You'll learn to secure apps, not just networks, making your skills invaluable in today's tech landscape.
🔒 Benefits in a Nutshell: ✅ Tighter Security ✅ Granular Access Control ✅ User-Centric Approach ✅ Enhanced Flexibility ✅ Improved User Experience
Following Vendors offer ZTNA
| Vendor | Solution | Key Features | Deployment | Integration |
| Palo Alto Networks | Prisma Access | Cloud-delivered security, granular access | Cloud-based | Integration with |
| policies, user and device verification | Palo Alto | |||
| Cisco | Zero Trust Security | Secure access, micro-segmentation, | On-premises, | Integration with |
| adaptive policies | Cloud-based | Cisco | ||
| Zscaler | ZPA | Application-centric, context-aware access | Cloud-based | Integration with |
| policies, user identity verification | identity providers | |||
| Akamai | Enterprise App | Secure application access, | Cloud-based | Integration with |
| Access | zero-trust approach | Akamai | ||
| Cloudflare | Cloudflare Access | Identity-based access, application-level | Cloud-based | Integration with |
| security | Cloudflare | |||
| Appgate | Appgate SDP | Dynamic segmentation, user context-based | On-premises, | Integration with |
| access policies | Cloud-based | existing network | ||
| Pulse Secure | Pulse Zero Trust | Secure access, unified policy enforcement, | On-premises, | Integration with |
| Access | context-aware authentication | Cloud-based | Pulse Secure | |
| Cato Networks | Cato Cloud | Unified security and networking platform, | Cloud-based | Integration with |
| context-based access policies | Cato Cloud | |||
| Forcepoint | Dynamic Edge | Risk-based access, user behavior analysis, | Cloud-based, | Integration with |
| Protection | application and data protection | On-premises | Forcepoint | |
| Barracuda Networks | CloudGen Access | Identity-based access, contextual security | Cloud-based | Integration with |
| policies | Barracuda |