Old vs New: How Cloud Security and Cloud Networking Are Replacing Traditional Networking
Mechanical Engineer by qualification with a strong passion for technology and networking. CCIE Routing & Switching and Security (#22239, since 2008). Former Cisco TAC, HP, and Wipro. Currently focused on building free, impactful tools for India. Ongoing projects include Namohos.com, Anantaos.com, and Freefreecv.com.
Networking is dead, yes almost.
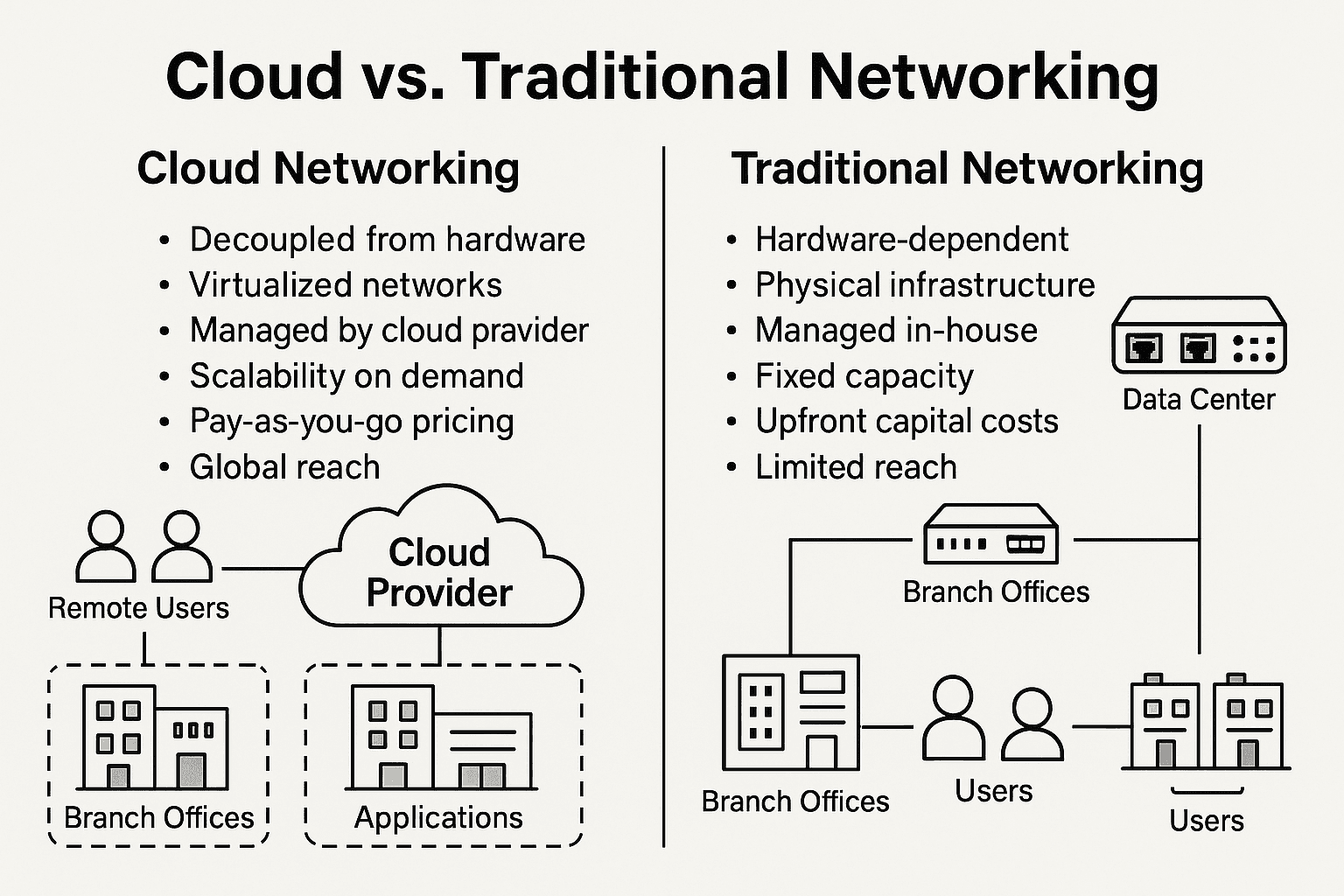
Over the last few years—but especially in the past 18 months—the networking and security landscape has shifted more dramatically than it did in the previous two decades. The trend is unmistakable: technologies that once required racks of on-prem appliances are being replaced by cloud-native services, and the job market is following this shift at high speed.
Last month, when I used data-science methods to analyze my company’s placement statistics, the results were unexpectedly clear. About 60% of our highest-paying offers for freshers (₹8.5L to ₹12.5L) came from companies hiring for cloud security products such as cloud firewalls, cloud gateways, secure access platforms, and cloud-native threat protection systems. Companies like Barracuda, Check Point, Zscaler, Palo Alto, and Skyhigh were consistently recruiting freshers specifically for roles tied to cloud security.
In comparison, only 20% of the opportunities were for pure traditional networking roles such as on-prem firewall management, router/switch support, or appliance-based network operations.
This blog explains why this shift is happening, which technologies are replacing older networking components, and what engineers—both freshers and experienced professionals—should know to remain relevant in this new cloud-first world.
Why the Shift Is Happening
1. Workloads Have Moved to the Cloud
Applications and data no longer sit inside a central data center. Organizations run workloads across AWS, Azure, GCP, and SaaS platforms. When apps move to the cloud, the networking model must follow. Traditional designs—routing all traffic through a data center for security inspection—add latency, cost, and complexity.
Cloud-native security places inspection and policy enforcement at the nearest cloud edge, not on an on-prem firewall box.
2. Remote Work Has Become the Default
The global shift to hybrid and remote work completely breaks the classic perimeter model. Employees connect from homes, co-working spaces, coffee shops, even mobile networks.
VPN concentrators and MPLS circuits were designed for office-centric traffic. They buckle under modern distributed workload patterns.
Cloud security platforms allow secure access from anywhere without forcing traffic through bottlenecks.
3. Cost and Operational Pressure
Traditional networking is expensive to scale:
MPLS links cost far more than broadband.
On-prem appliances require refresh cycles, patches, and physical maintenance.
Disaster recovery requires duplicate hardware.
Cloud architectures reduce operational overhead:
No hardware refresh.
Lower cost per user.
Rapid onboarding of new sites without waiting for leased line provisioning.
4. Zero Trust Is Becoming Standard
The security industry is moving away from “inside = trusted.”
Zero Trust designs require:
identity-based access
device posture checks
microsegmented permissions
continuous verification
This model cannot be achieved effectively with legacy firewalls or traditional VPNs. It aligns much more naturally with cloud-delivered security platforms such as ZTNA and SASE.
5. The Rise of Integrated Cloud Platforms (SASE and SSE)
Modern security stacks combine multiple functions—firewall, proxy, CASB, ZTNA—into one cloud-native architecture.
This avoids the sprawl of appliances and point solutions and allows centralized, unified policy.
6. Cloud Telemetry, Observability, and Automation
Cloud platforms capture detailed logs, user behavior telemetry, network flow analytics, and API-driven metrics. Modern engineers need to analyze, automate, and optimize distributed systems—skills that simply do not exist in traditional box-based networks.
Your own use of data science to study placement trends is an example of how analytics itself has become a valuable engineering skill.
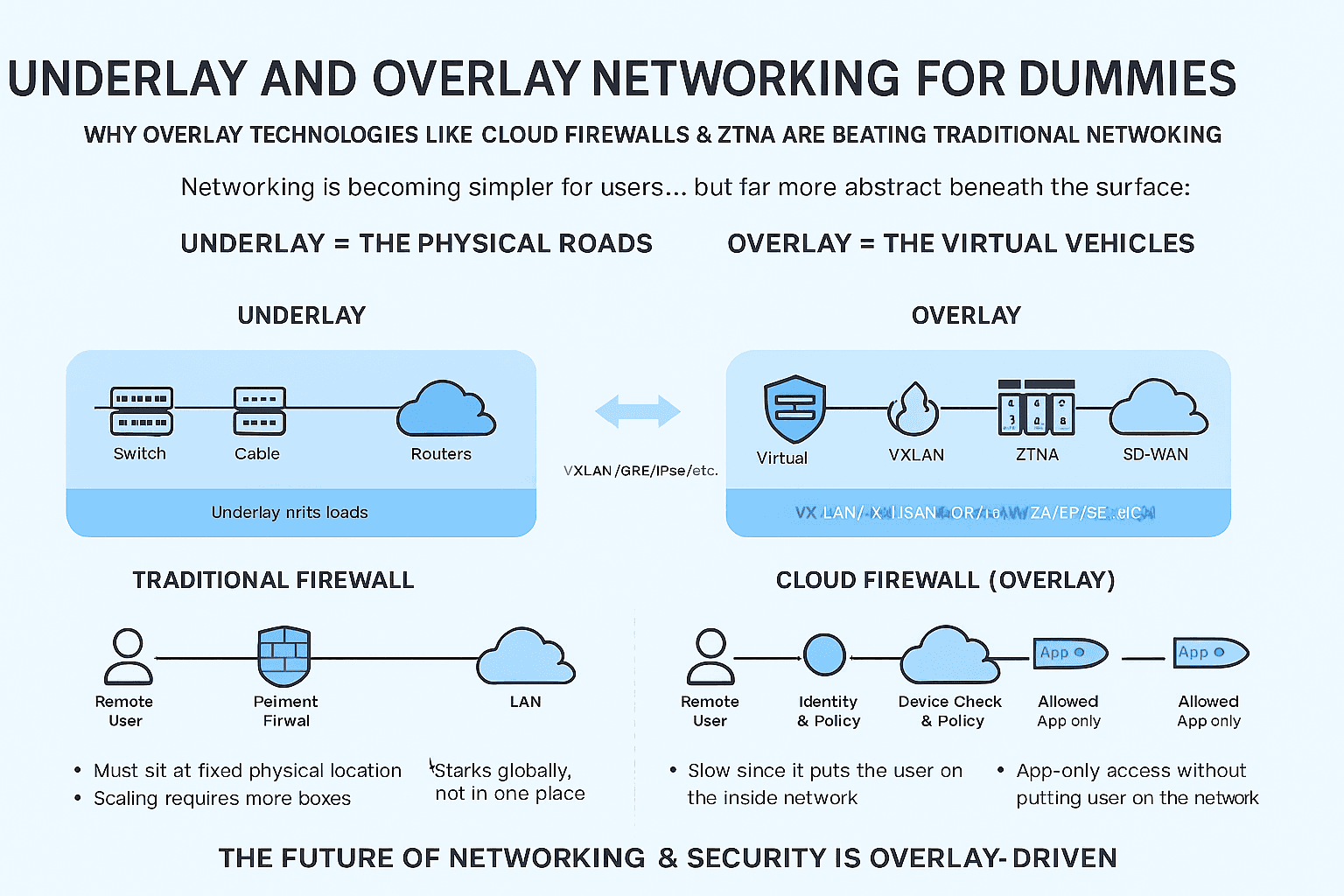
What Is Being Replaced, and By What
Below is a clear mapping of old networking technologies and the cloud technologies that replace them.
1. MPLS WAN → SD-WAN and SASE
Traditional MPLS:
Expensive private links
Slow to provision
Traffic hairpinned to data centers
Not optimized for cloud or SaaS
Replaced by:
SD-WAN: intelligent path selection, broadband + LTE + MPLS mix, centralized orchestration
SASE: SD-WAN + cloud firewall + ZTNA + secure web gateway in a unified cloud architecture
Organizations adopt SD-WAN to reduce costs and adopt SASE to add cloud-native security on top of it.
2. On-Prem Firewalls → Firewall-as-a-Service (FWaaS) and Cloud Security Edge
Traditional firewalls:
Hardware appliances at branch and data center
Require manual updates and physical scaling
Perimeter model assumes all users are inside the network
Replaced by:
FWaaS: cloud-delivered firewall filtering all traffic at global edge locations
SASE: integrates FWaaS with secure access, data protection, and threat prevention
Cloud firewalls deliver policy enforcement close to users instead of forcing traffic through a central box.
3. VPN Concentrators → Zero Trust Network Access (ZTNA)
Traditional VPN:
Tunnel-based access
Gives users broad network access
Hard to scale for globally distributed teams
High latency and heavy maintenance
Replaced by:
ZTNA: identity-based, least-privilege, app-level access without network-level exposure
Sessions created dynamically per user and per application
No network-wide trust after login
ZTNA is now the industry standard for secure remote work.
4. On-Prem Web Proxies / Secure Web Gateways → Cloud SWG and CASB
Traditional proxies:
Hosted at branches or data centers
Struggle with SaaS and encrypted traffic
Not built for mobile users or dynamic cloud apps
Replaced by:
Cloud SWG: cloud-delivered web filtering, malware scanning, SSL inspection
CASB: controls SaaS usage, API-based monitoring, data protection
SSE: unified delivery of SWG, CASB, and ZTNA in a cloud-native architecture
Cloud SWGs ensure users get identical security controls anywhere in the world.
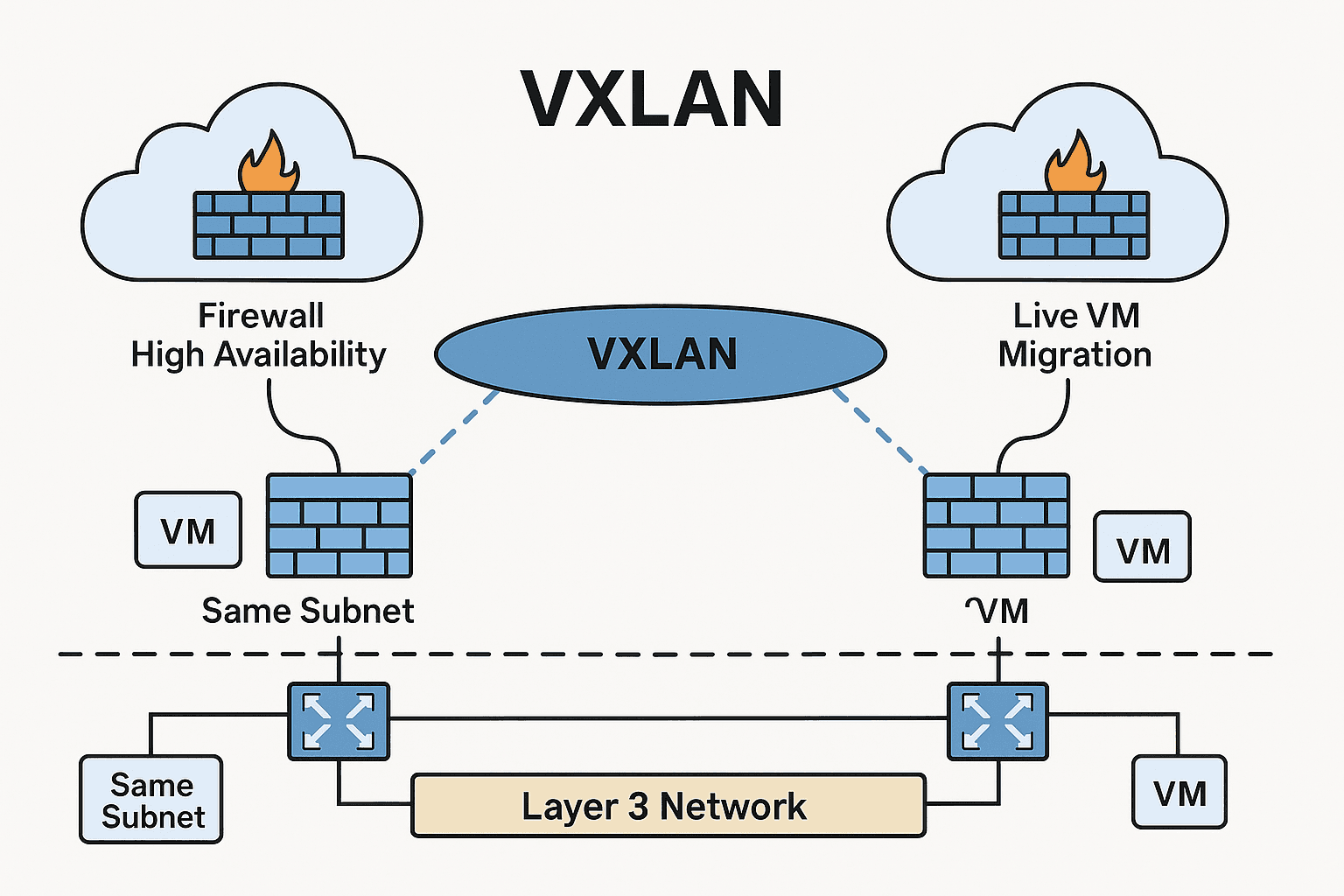
5. Hardware Load Balancers / ADC → Cloud Load Balancers & Service Mesh
As applications move to Kubernetes, serverless, and distributed microservices, older hardware ADCs lose relevance.
Cloud platforms now provide:
global load balancing
API gateways
service mesh for microservice traffic
autoscaling and failover
These cloud tools remove the need for manual hardware tuning.
6. Network Access Control (NAC) → Identity and Endpoint-based Access
Old NAC systems depended on:
VLAN assignments
device profiling via MAC
switch port-level control
This model does not work for remote/multi-device users.
Replaced by:
cloud identity platforms (Azure AD, Okta, Google IAM)
endpoint posture checks through device agents
integrated decisions feeding ZTNA/SASE platforms
Identity becomes the primary perimeter.
How This Shift Affects Careers
Skills That Matter Now
Cloud Networking
VPC/VNet design
routing in cloud
virtual gateways
cloud load balancing
peering, transit gateways
Cloud Security & Zero Trust
SASE, SSE, FWaaS
ZTNA configuration
SWG/CASB use cases
identity-driven access
Automation & DevOps
Terraform
Python/Shell scripting
CI/CD for network/security configs
Observability & Data
cloud logging and flow analytics
SIEM
packet/HTTP analysis
telemetry dashboards
Cloud Platforms
AWS, Azure, GCP networking & security services
cloud IAM
monitoring and configuration frameworks
Freshers with hands-on cloud labs outperform candidates who only studied routers, switches, and firewalls.
What Companies Are Looking For
Engineers who understand cloud and networking together, not separately.
Ability to work with SASE, SD-WAN, ZTNA, FWaaS, CASB tools.
Comfort with automation instead of manual CLI configuration.
Skill in analyzing logs, telemetry, and data patterns.
Ability to secure modern SaaS-driven environments.
Traditional “network support engineer” roles are being replaced by “cloud network engineer,” “cloud security engineer,” and “SASE engineer.”